What is Password Cracking?
Password cracking is the process of attempting to gain Unauthorized access to restricted systems using common passwords or algorithms that guess passwords. In other words, it's an art of obtaining the correct password that gives access to a system protected by an authentication method.
Password cracking employs a number of techniques to achieve its goals. The cracking process can involve either comparing stored passwords against word list or use algorithms to generate passwords that match
In this Tutorial, we will introduce you to the common password cracking techniques and the countermeasures you can implement to protect systems against such attacks.
Topics covered in this tutorial
What is password strength?
Password strength is the measure of a password's efficiency to resist password cracking attacks. The strength of a password is determined by;
- Length: the number of characters the password contains.
- Complexity: does it use a combination of letters, numbers, and symbol?
- Unpredictability: is it something that can be guessed easily by an attacker?
Let's now look at a practical example. We will use three passwords namely
1. password
2. password1
3. #password1$
For this example, we will use the password strength indicator of Cpanel when creating passwords. The images below show the password strengths of each of the above-listed passwords.
Note: the password used is password the strength is 1, and it's very weak.
Note: the password used is password1 the strength is 28, and it's still weak.
Note: The password used is #password1$ the strength is 60 and it's strong.
The higher the strength number, better the password.
Let's suppose that we have to store our above passwords using md5 encryption. We will use an online md5 hash generator to convert our passwords into md5 hashes.
The table below shows the password hashes
| Password | MD5 Hash | Cpanel Strength Indicator |
|---|
| password | 5f4dcc3b5aa765d61d8327deb882cf99 | 1 |
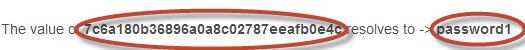
| password1 | 7c6a180b36896a0a8c02787eeafb0e4c | 28 |
| #password1$ | 29e08fb7103c327d68327f23d8d9256c | 60 |
We will now use http://www.md5this.com/ to crack the above hashes. The images below show the password cracking results for the above passwords.
As you can see from the above results, we managed to crack the first and second passwords that had lower strength numbers. We didn't manage to crack the third password which was longer, complex and unpredictable. It had a higher strength number.
Password cracking techniques
There are a number of techniques that can be used to crack passwords. We will describe the most commonly used ones below;
- Dictionary attack– This method involves the use of a wordlist to compare against user passwords.
- Brute force attack– This method is similar to the dictionary attack. Brute force attacks use algorithms that combine alpha-numeric characters and symbols to come up with passwords for the attack. For example, a password of the value "password" can also be tried as p@$$word using the brute force attack.
- Rainbow table attack– This method uses pre-computed hashes. Let's assume that we have a database which stores passwords as md5 hashes. We can create another database that has md5 hashes of commonly used passwords. We can then compare the password hash we have against the stored hashes in the database. If a match is found, then we have the password.
- Guess– As the name suggests, this method involves guessing. Passwords such as qwerty, password, admin, etc. are commonly used or set as default passwords. If they have not been changed or if the user is careless when selecting passwords, then they can be easily compromised.
- Spidering– Most organizations use passwords that contain company information. This information can be found on company websites, social media such as facebook, twitter, etc. Spidering gathers information from these sources to come up with word lists. The word list is then used to perform dictionary and brute force attacks.
Spidering sample dictionary attack wordlist
1976 <founder birth year>
smith jones <founder name>
acme <company name/initials>
built|to|last <words in company vision/mission>
golfing|chess|soccer <founders hobbies
Password cracking tool
These are software programs that are used to crack user passwords. We already looked at a similar tool in the above example on password strengths. The website www.md5this.com uses a rainbow table to crack passwords. We will now look at some of the commonly used tools
John the Ripper
John the Ripper uses the command prompt to crack passwords. This makes it suitable for advanced users who are comfortable working with commands. It uses to wordlist to crack passwords. The program is free, but the word list has to be bought. It has free alternative word lists that you can use. Visit the product website http://www.openwall.com/john/ for more information and how to use it.
Cain & Abel
Cain & Abel runs on windows. It is used to recover passwords for user accounts, recovery of Microsoft Access passwords; networking sniffing, etc. Unlike John the Ripper, Cain & Abel uses a graphic user interface. It is very common among newbies and script kiddies because of its simplicity of use. Visit the product website http://www.softpedia.com/get/Security/Decrypting-Decoding/Cain-and-Abel.shtml for more information and how to use it.
Ophcrack
Ophcrack is a cross-platform Windows password cracker that uses rainbow tables to crack passwords. It runs on Windows, Linux and Mac OS. It also has a module for brute force attacks among other features. Visit the product website http://ophcrack.sourceforge.net/ for more information and how to use it.
Password Cracking Counter Measures
- An organization can use the following methods to reduce the chances of the passwords been cracked
- Avoid short and easily predicable passwords
- Avoid using passwords with predictable patterns such as 11552266.
- Passwords stored in the database must always be encrypted. For md5 encryptions, its better to salt the password hashes before storing them. Salting involves adding some word to the provided password before creating the hash.
- Most registration systems have password strength indicators, organizations must adopt policies that favor high password strength numbers.
Hacking Activity: Hack Now!
In this practical scenario, we are going to crack Windows account with a simple password. Windows uses NTLM hashes to encrypt passwords. We will use the NTLM cracker tool in Cain and Abel to do that.
Cain and Abel cracker can be used to crack passwords using;
- Dictionary attack
- Brute force
- Cryptanalysis
We will use the dictionary attack in this example. You will need to download the dictionary attack wordlist here 10k-Most-Common.zip
For this demonstration, we have created an account called Accounts with the password qwerty on Windows 7.
Password cracking steps
- Open Cain and Abel, you will get the following main screen
- Make sure the cracker tab is selected as shown above
- Click on the Add button on the toolbar.
- The following dialog window will appear
- The local user accounts will be displayed as follows. Note the results shown will be of the user accounts on your local machine.
- Right click on the account you want to crack. For this tutorial, we will use Accounts as the user account.
- The following screen will appear
- Right click on the dictionary section and select Add to list menu as shown above
- Browse to the 10k most common.txt file that you just downloaded
- Click on start button
- If the user used a simple password like qwerty, then you should be able to get the following results.
- Note: the time taken to crack the password depends on the password strength, complexity and processing power of your machine.
- If the password is not cracked using a dictionary attack, you can try brute force or cryptanalysis attacks.
Summary
- Password cracking is the art of recovering stored or transmitted passwords.
- Password strength is determined by the length, complexity, and unpredictability of a password value.
- Common password techniques include dictionary attacks, brute force, rainbow tables, spidering and cracking.
- Password cracking tools simplify the process of cracking passwords.
@EVERYTHING NT
Read more